The following steps are outlined in kb article 87098. Hence the reason for the upgrade to 8.5.0.2.
CVE-2021-44228 has been determined to impact Site Recovery Manager and vSphere Replication via the Apache Log4j open source component it ships. This vulnerability and its impact on VMware products are documented in the following VMware Security Advisory (VMSA), please review this document before continuing:
- CVE-2021-44228 – VMSA-2021-0028
You can validate exposure on a replication/site recovery appliance by running the following command from a shell as the root user:
grep -R 'JndiLookup.class' /opt/vmware/
grep -R 'JndiLookup.class' /var/opt/apache-tomcat/cd ..
If the mitigation has been successfully applied these command will not return results. If else you will see:
root@vcsa [ / ]# grep -R 'JndiLookup.class' /opt/vmware/
Binary file /opt/vmware/lib64/log4j-core-2.13.0.jar matches
grep: /opt/vmware/vpostgres/12/lib-private/liblber.so: No such file or directory
grep: /opt/vmware/vpostgres/12/lib-private/libldap.so: No such file or directory
grep: /opt/vmware/vpostgres/12/lib-private/libldap_r.so: No such file or directory
What’s New in VMware Site Recovery Manager 8.5.0.2
You can check the release notes here.
Basically, it contains the updated Apache log4j to version 2.16 to resolve CVE-2021-44228 and CVE-2021-45046. For more information on these vulnerabilities and their impact on VMware products, see VMSA-2021-0028.
Preperations
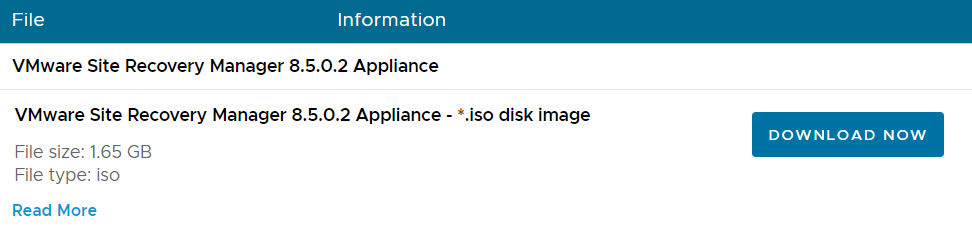
- Download the .iso update file at VMware.
- Export the SRM configuration file > Within Site Recovery Manager go to Summary

Export the SRM configuration

- Make a snapshot of the SRM appliances
- SRM does not save custom settings within ‘Advanced Settings’. Make sure that you take note of each individual setting at SRM > Configure > Advanced Settings
- Check if there are no pending clean-up jobs in the ‘Recovery Plans’ section
- Check whether there are configuration issues for the VM’s that SRM protects
- Check if all ‘Recovery Plans’ have the ‘Ready State’
- Check if the ‘Protection Status’ all the ‘Protection Groups’ is OK
- Check if the ‘Protection Status’ of all VM’s in the ‘Potection Groups’ is OK
- Check if the ‘Recovery Status’ of all ‘Protection Groups’ is ‘Ready’
Upgrade Procedure
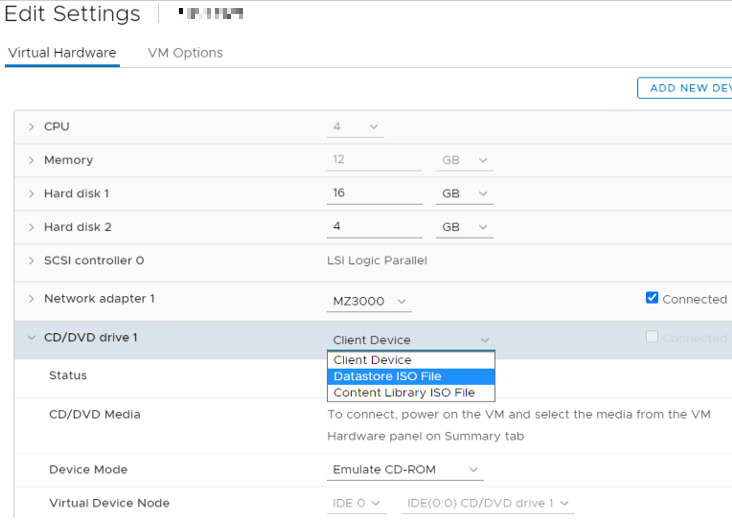
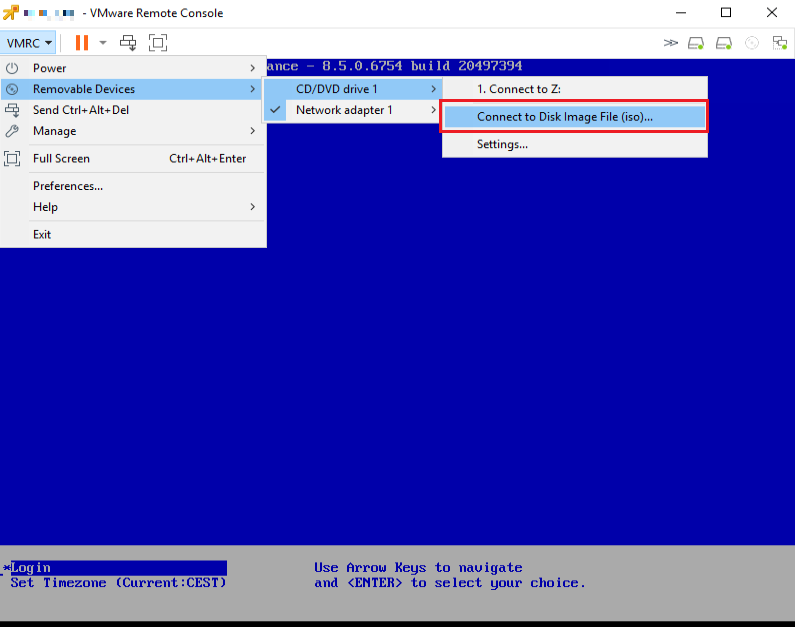
Add the .iso file to the VM via whichever method you prefer
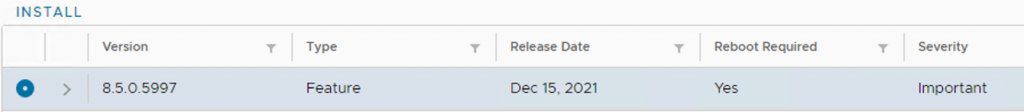
(The buildnumber in the below screenshot is higher because it is from a recent update)
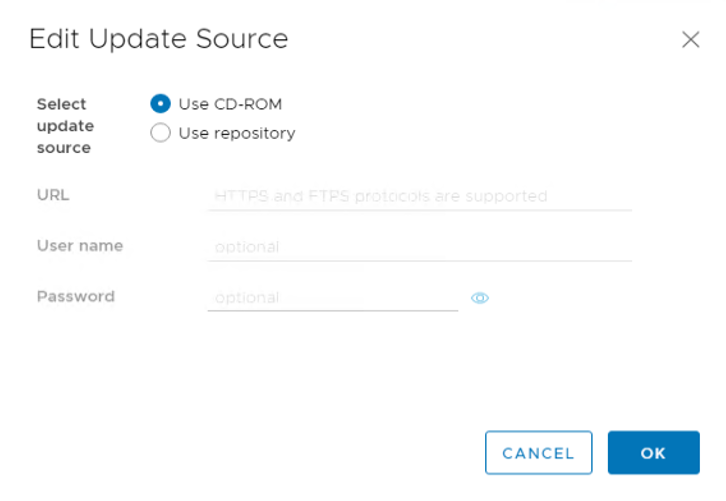
Log in to the SRM appliance VAMI web interface, navigate to ‘ Update’ to ‘ Edit’ the ‘Update Source’
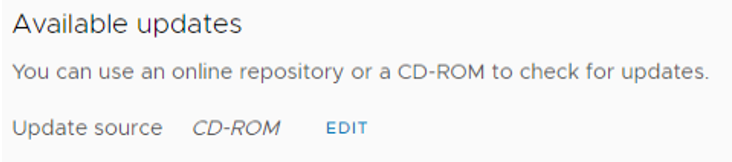
Select ‘ Use CD-ROM’
Select ‘Install’
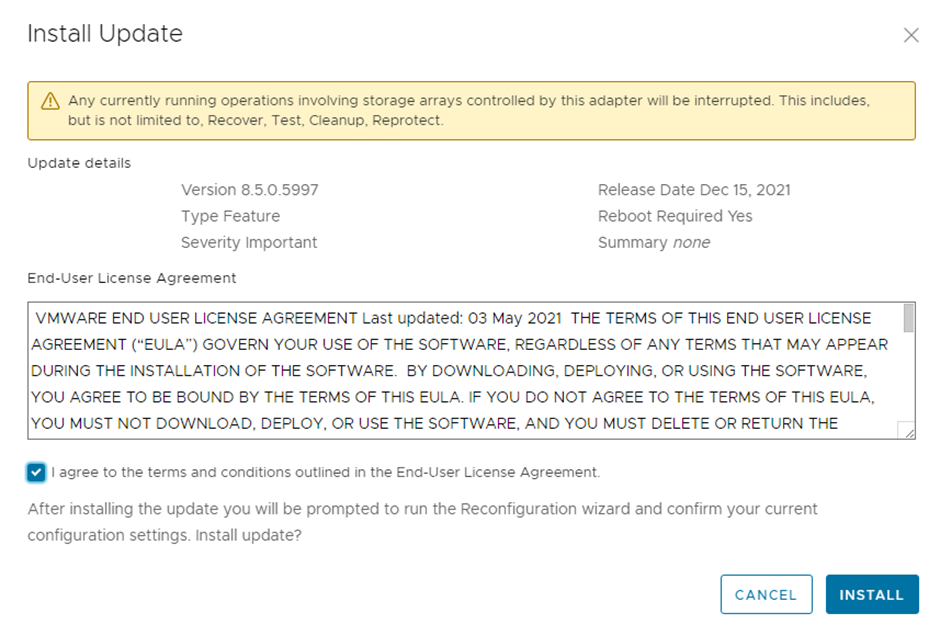
Agree with the terms and select ‘Install’

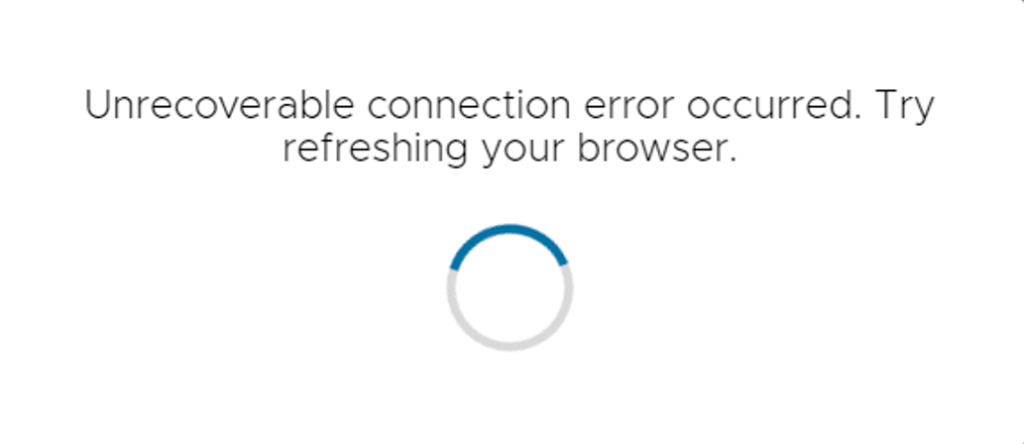
If you get the below error message then refresh your browser. The update continues on the background.
After the update is finished, log back into the SRM VAMI and select ‘Reconfigure’

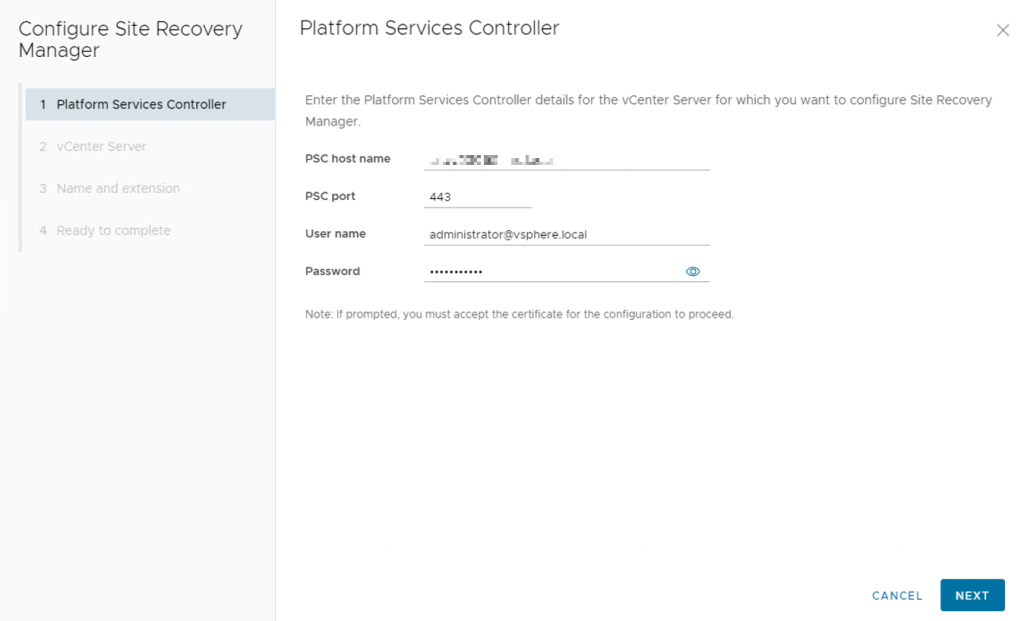
Put in the credentials
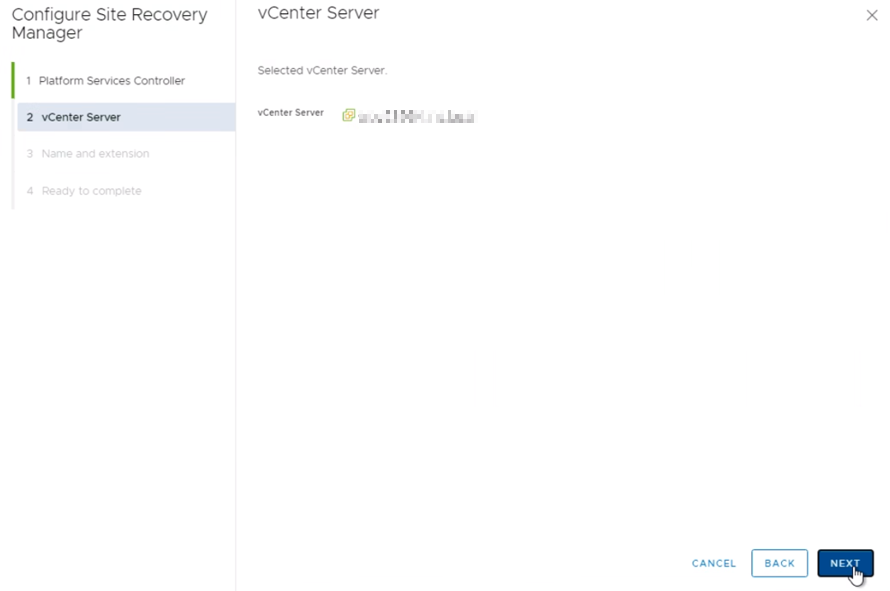
Next
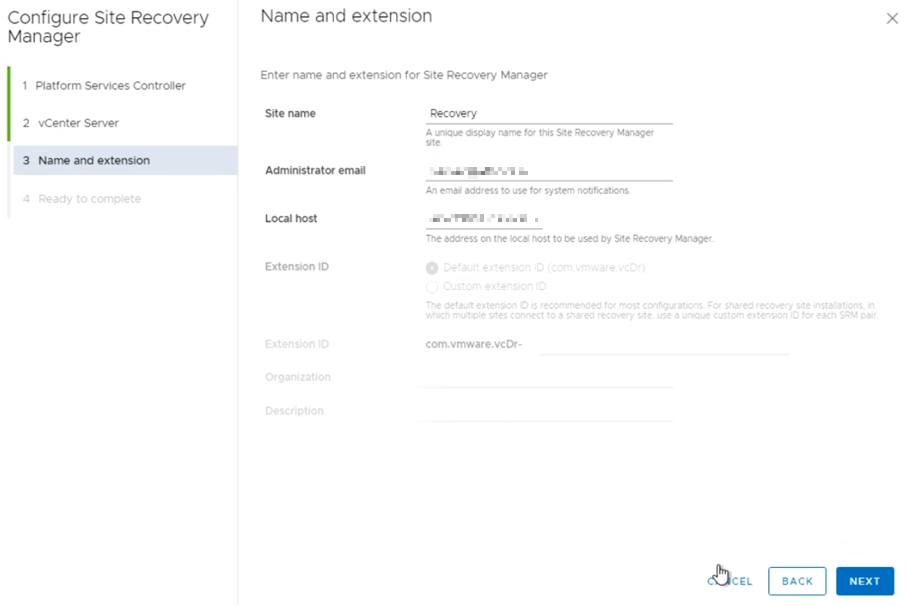
Update is finializing

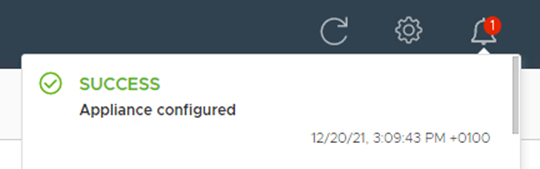
Update is successful.
About Site Recovery
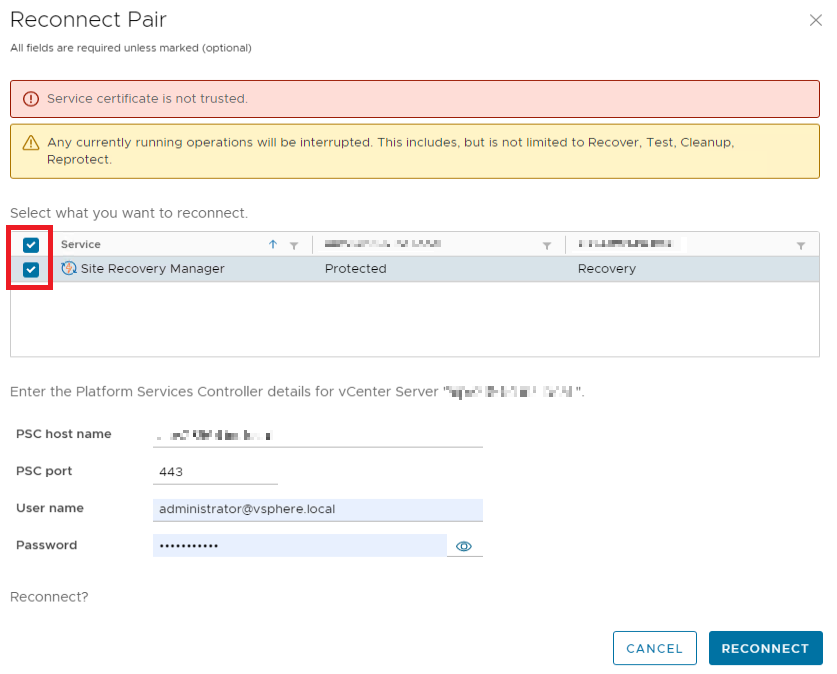
If you have a site pair, then log into your SRM Appliance Management UI and perform a ‘Reconnect Pair’.
As a final step, navigate to the SRM web Interface and do the same aforementioned checks to see if there are no error messages displayed.